Elrik said:
I'm not a security IT professional
Which is exactly why you shouldn't be finetuning TOR browser security settings.
Elrik said:
and I'm not a paranoid that checks every setting every time TBB starts
If you use TOR, and the impenetrability of your anonymous identity is important to you, a certain degree of paranoia is warranted. Then again, it would seem from your posts that you show a degree of paranoia where it's not rational, and lack it where it would be rational.
Elrik said:
nor am I a dim wit, I'm just your average TOR user who is using it for nexus type things and chemistry research.
Never said you were a dimwit, I'm just saying you're arguing about things you lack full understanding of, and therefore using flawed grounds for your arguments and actions.
Elrik said:
After logging in to several sites I noticed that scripts which I had forbidden ever since starting TOR 2 years before were running.
And what scripts are those?
Elrik said:
I had gone half the way across the net with no security at all, beyond TORs inherent proxies.
No security at all? That sounds like a grand statement from someone who admittedly doesn't fully understand security. I can assure you that you were protected by an adequate level of security for the use case of "nexus type things and chemistry research".
Now, federal agents wiretapping you personally, using zero-day browser exploits and government sponsored malware, that's an entirely different threat model, but let's hope you don't have that kind of heat on you.
The latest TBB is safe with its default in that no public exploit exists that would allow either high accuracy fingerprinting, or an unmasking of your real IP address, or accessing your hard drive, without active participation on your part (such as downloading and running malware outside the TOR browser).
You're safe.
Manually forbidding Russian ad scripts (perfectly harmless within the sandbox of the TOR browser) can, however, work against you by creating a unique browser fingerprint.
Elrik said:
It was impossible to forbid scripts globally in the usual way but I eventually found where to redefine the default from allow-everything to block.
Onion button > Security settings > "Safest"
That's it. Done.
Elrik said:
I thought I had it fixed so I moved on. The next day I started it up and logged into a site and went to download a paper and russian AD panes I had never seen before popped up, thats when I discovered that, without warning the user, user customized security settings are reset on every program start- with no apparent way to fix it.
That is a feature. Persistent unique settings will allow an attacker to generate a fingerprint of your browser, allowing you to be tracked throughout all your TOR operations. Disabling the persistence of user customizations and starting from a clean slate each time is actually very important for real (as opposed to imaginary) security.
Elrik said:
So they changed peoples security radically without clear warning, and then did it yet again. They knowingly compromised peoples usual security measures and did so more or less covertly.
They compromised imaginary and wrong security measures in favor of implementing a real security measure.
Elrik said:
That is what I call insecure.
And that is where you are wrong.
Elrik said:
Now that I know about these issues I can browse without being tricked by those issues again, but its very tempting to just roll back to 7.5.6 until persistent user defined security settings are allowed.
As I said, you are again paranoid where you shouldn't be, and ignoring real danger. Old versions of the TBB may have public exploits that allow the real IP address to be unmasked by a malicious site. Not all malware can be disabled by forbidding scripts.
Also, as I said, persistent user settings are insecure.
Elrik said:
I can understand their reason for changing the default, but the warnings should have been noticeable and their idea of security settings should be optional.
It is optional.
Again,
Onion button > Security settings > "Safest"
Elrik said:
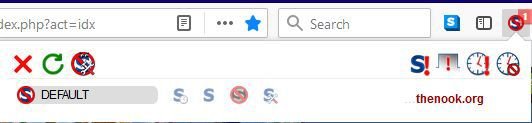
To clarify what I mean about the deceptive block icon, observe this pic. It says 'default' with the icon for block-all, while 'default' is actually the same as allow-all [a different icon].
Yea I'm not a huge fan of NoScript's interface, I'll give you that. But in the TBB, you're not supposed to use that interface, you're supposed to use
Onion button > Security settings